Configuring Ansible Dynamic Inventory aws_ec2 plugin
We already know how to connect to AWS instance using SSH over AWS SSM, so we are ready to go one step forward and connect to EC2 instances utilizing Ansible dynamic inventory aws_ec2 plugin. It allows us to work with tags rather than EC2 instance IDs or IP addresses. This is very handy when managing instances withing Auto Scaling Groups where EC2 instances are being created and terminated automatically and IP addresses are not persistent.
Configuring Ansible aws_ec2 plugin
aws_ec2 – EC2 inventory source plugin let us create inventory hosts from AWS EC2. It uses a YAML configuration file that ends with .aws_ec2.yml e.g. inventory.aws_ec2.yml
To enable it, edit ansible.cfg file (e.g. in your project dir) and add the following line:
[inventory] enable_plugins = aws_ec2
Next, create a YAML configuration file inventory.aws_ec2.yml and save it in e.g. <ansible_project>/inventory/dev directory. Note that the name of the file must end exactly .aws_ec2.yml.
<ansible_project>/inventory/dev/inventory.aws_ec2.yml
Assuming that we have an active session to our AWS account, we are ready to test our scenario:
$ cd <ansible_project> $ ansible-inventory -i inventories/dev/inventory.aws_ec2.yml --graph @all: |--@aws_ec2: | |--i-01db65678937d3ff8 | |--i-02e333hdsjk55d950 |--@tag_Name_MasterNodes: | |--i-0a45925d69852cbf7 |--@tag_Name_SlaveNodes: | |--i-01vf87653998d3ff8 | |--i-31a878777499b62c0 |--@tag_Name_WebServers: | |--i-045dde6ed8ad1bfec |--@ungrouped:
In a result, we see EC2 instance tags and respective IDs with a prefix “tag_Name_”, that’s the tag that we can use in our playbooks.
For example:
$ cd <ansible_project>
$ ansible -i inventories/dev/inventory.aws_ec2.yml tag_Name_SlaveNodes -u ec2-user -m 'ping'
--i-01vf87653998d3ff8 | SUCCESS => {
"ansible_facts": {
"discovered_interpreter_python": "/usr/bin/python"
},
"changed": false,
"ping": "pong"
}
i-31a878777499b62c0 | SUCCESS => {
"ansible_facts": {
"discovered_interpreter_python": "/usr/bin/python"
},
"changed": false,
"ping": "pong"
}
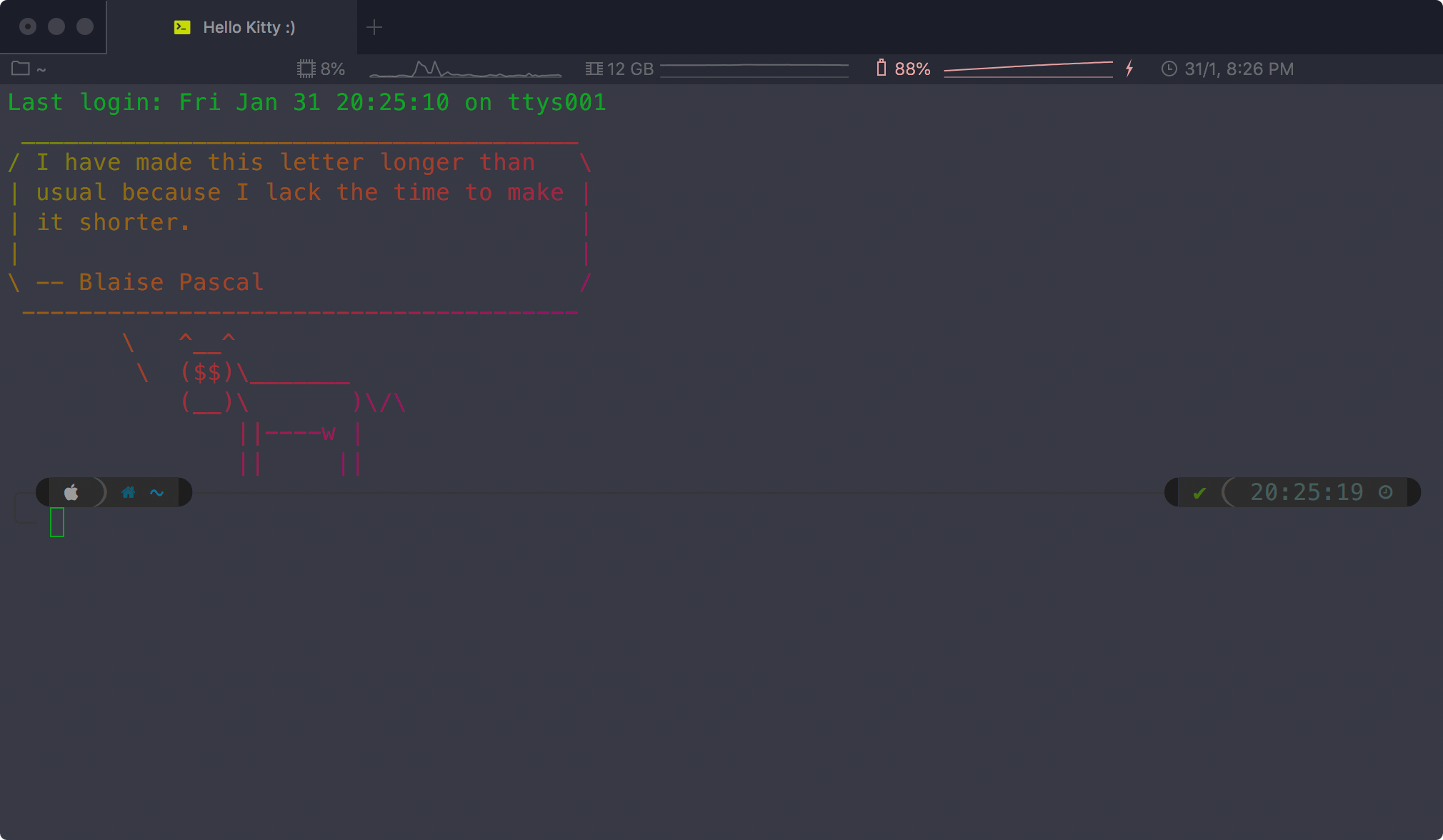
$ ansible -i inventories/dev/inventory.aws_ec2.yml tag_Name_SlaveNodes -u ec2-user -m sheel -a 'echo "Hello Kitty"'
i-01vf87653998d3ff8 | CHANGED | rc=0 >>
Hello Kitty
i-31a878777499b62c0 | CHANGED | rc=0 >>
Hello Kitty
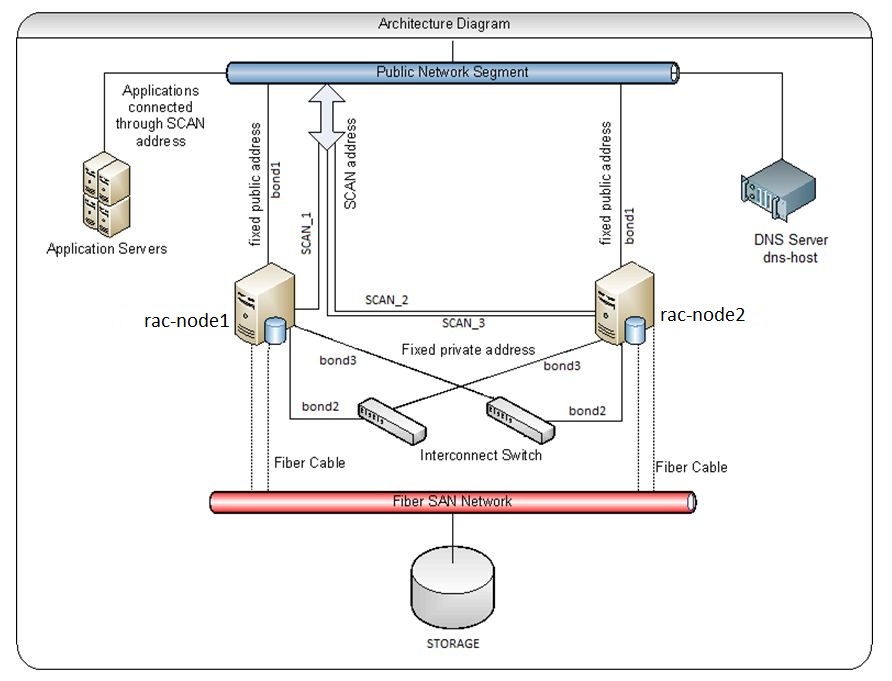
For Ansible it is SSH while the connection is going over AWS SSM proxy, which we have configured in our .ssh/config file:
cat ~/.ssh/config host i-* mi-* 10. User ec2-user ProxyCommand sh -c "export AWS_PROFILE=<profile_name>; aws ssm start-session --target %h --document-name AWS-StartSSHSession --parameters 'portNumber=%p'" IdentityFile ~/.ssh/aws-key.pem
Cheers!!